Dear Readers,
In this blog we are going to learn about, Triple Data Encryption Standard (3DES), a cryptographic algorithm descended from the original Data Encryption Standard (DES), made its debut in 1998 and has long served as a stalwart protector of data in the realms of finance and private industry, securing both data-at-rest and data-in-transit. Nevertheless, the prominence of 3DES has waned over time due to the ascent of more formidable encryption methods such as AES-256 and XChaCha20. As it approaches official deprecation in 2023, 3DES continues to find use in select scenarios. This article delves into the world of 3DES, exploring its history, variations, current status, and application methods, shedding light on its role in the evolving landscape of data security.
3DES is an encryption cipher derived from the original Data Encryption Standard (DES). 3DES was first introduced in 1998, the algorithm is primarily adopted in finance and other private industry to encrypt data-at-rest and data-in-transit. It became prominent in the late nineties but has since fallen out of favor due to the rise of more secure algorithms, such as AES-256 and XChaCha20. Although it will depreciate in 2023, it’s still implemented in some situations.
About Triple DES or 3DES
The Triple DES (often referred to as Data Encryption Algorithm (TDEA)) is specified in SP 800-6711 107 and has two variations, known as two-key TDEA and 108 three-key TDEA. Three-key TDEA is the stronger of the two variations.Below is the status of the 3DES algorithm used for encryption and decryption
| Algorithm | Status |
|---|---|
| Two-key TDEA Encryption | Disallowed |
| Two-key TDEA Decryption | Legacy use |
| Three-key TDEA Encryption | Deprecated through 2023Disallowed after 2023 |
| Three-key TDEA Decryption | Legacy use |
Three-key TDEA encryption and decryption
Effective as of the final publication of this revision of SP 800-131A, encryption using three-key TDEA is deprecated through December 31, 2023, using the approved encryption modes. Note that SP 800-67 specifies a restriction on protecting no more than 220 data blocks using the same single key bundle. Three-key TDEA may continue to be used for encryption in existing applications but shall not be used for encryption in new applications. After December 31, 2023, three-key TDEA is disallowed for encryption unless specifically allowed by other NIST guidance. Decryption using three-key TDEA is allowed for legacy use.
How is Triple DES/3DES applied?
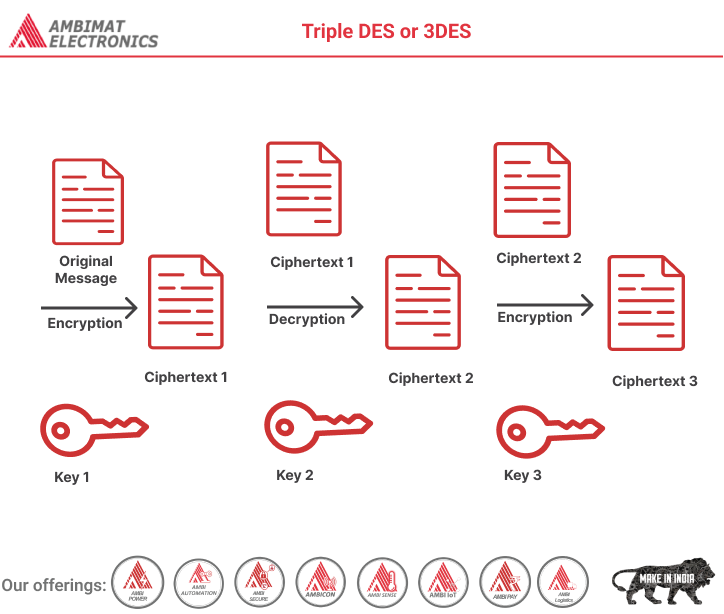
Triple DES is a type of encryption that employs three DES instances on the same plaintext. It employs a variety of key selection approaches, including the following:
- all utilized keys are different in the first
- two keys are the same and one is different in the second
- and all keys are the same in the third.
About Ambimat Electronics:
With design experience of close to 4 decades of excellence, world-class talent, and innovative breakthroughs, Ambimat Electronics is a single-stop solution enabler to Leading PSUs, private sector companies, and start-ups to deliver design capabilities and develop manufacturing capabilities in various industries and markets. AmbiIoT design services have helped develop Smartwatches, Smart homes, Medicals, Robotics, Retail, Pubs and brewery, Security.
Ambimat Electronics has come a long way to become one of India’s leading IoT(Internet of things) product designers and manufacturers today. We present below some of our solutions that can be implemented and parameterized according to specific business needs. AmbiPay, AmbiPower, AmbiCon, AmbiSecure, AmbiSense, AmbiAutomation.
To know more about us or what Ambimat does, we invite you to follow us on LinkedIn or visit our website.