Dear Readers,
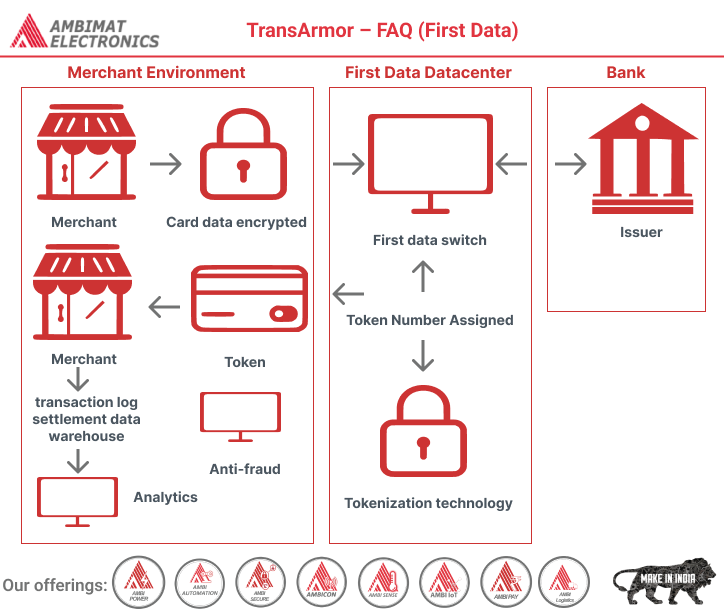
In this blog we are going to learn about, The TransArmor Solution represents a robust and comprehensive payment card security system that marries advanced encryption and tokenization technologies to safeguard sensitive transaction data. From the moment a payment card is swiped, TransArmor ensures the data remains encrypted throughout the entire payment process, preventing any exposure within the merchant’s card data environment. This innovative solution replaces the primary account number (PAN) with a randomly generated token, enhancing security and facilitating compliance with PCI standards. Offering multiple encryption methods, TransArmor empowers merchants to reduce risk, lower PCI compliance costs, and securely protect cardholder data. Supporting TransArmor involves adhering to First Data specifications, with potential implications for PA-DSS/PCI compliance, ensuring a safer and more secure payment ecosystem for both merchants and consumers.
1. What is the TransArmor Solution?
TransArmor is a dual-layered payment card security solution that combines strong encryption
and tokenization technology. TransArmor secures the transaction from the moment of swipe –
prior to transmission and throughout the payment process with encryption, and it prevents
card data from entering the merchant’s card data environment (CDE) by replacing the primary
account number (PAN) with a random-number token that can be safely stored.
2. How Does TransArmor Work in a Card-Present Environment?
- Consumer presents card to merchant
- Card Data is encrypted and transmitted to First Data front-end
- First Data front-end decrypts the data payload
- Card data is sent to issuing bank for authorization and in parallel, tokenized
- Token is paired with authorization response and sent back to the merchant
- Merchant stores token instead of card data in their environment and uses token for all subsequent business processes
3. What Encryption Methods are Used in TransArmor?
There are four available encryption methods used in TransArmor: Three are Symmetric (shared key), and one is Asymmetric (public key).
TransArmor Verifone Edition (TAVE): Symmetric Key – Format Preserving Encryption (FPE)
• PAN and Discretionary data is encrypted
at read in tamper-resistant hardware
• Supports mag-stripe, RFID, smart-card
and manual entry
• Based on AES 128-bit algorithm
• FPE data resembles original target data
3DES: Symmetric Key – Non-Format Preserving Encryption (Non-FPE)
• 3DES is the common name for the Triple Data Encryption
Standard algorithm (symmetric-key block cipher)
• 3DES applies the Data Encryption Standard (DES) cipher
algorithm three times to each data block
• Supports mag-stripe, RFID, smart-card and manual entry
• 3DES keys must be loaded securely into the device either by
First Data Hardware Services (fka TASQ), an approved ESO
or through an approved Remote Key Injection method
• Non-FPE data does not resemble original target data
Ingenico On-Guard: Symmetric Key – Format Preserving Encryption (FPE)
• Ingenico’s proprietary Format Preserving Encryption is based
on the 3DES algorithm
• PAN, Track 1 and Track 2 data is encrypted at swipe in an
Ingenico device
• OnGuard 3DES keys must be loaded securely into the device
either by First Data Hardware Services (fka TASQ) or Ingenico
• Supports mag-stripe, RFID, smart-card and manual entry
• FPE data resembles original target data
RSA/PKI: Asymmetric Key – Non-Format Preserving Encryption (Non-FPE)
• Uses the RSA 2048-bit algorithm
• Public Key resides on merchant device
• Private Key resides within First Data data center
• Supports mag-stripe, RFID, smart-card and manual entry
• Non-FPE data does not resemble original target data
4. What is Tokenization?
• Tokenization is a form of data substitution
• TransArmor tokenization uses randomly generated numbers in place of PAN
• Tokenization differs from encryption: Tokens have no direct relationship with the data they replace
• TransArmor tokens are either universal or merchant-specific
• Tokens are card-based, meaning a merchant will always get the same token back for a specific PAN
5. As a Vendor, What Are the Benefits of Supporting TransArmor?
• Reduces the costs associated with PCI compliance in three ways:
1. Shrinks the vendors card-data environment (CDE)
2. Simplifies the questionnaire that the vendors customers must answer
3. Changes the answers of some questions to N/A
• Removes the risk of storing card data, transferring it to the processor
• Allows the vendor to focus on projects that contribute to revenue rather than securing cardholder data
6. How Do I Support TransArmor?
Listed below are the First Data specifications that support TransArmor:
BuyPass® – ATL105, Host/Controller, ISO8583
CARDnet® – ISO 8583 with and without PTS Settlement, EDC
Nashville – ISO 8583 with and without PTS Settlement
Compass – Batch/Online
Omaha – ETC+
7. Will I Need to Certify/Re-certify for PA-DSS/PCI Compliance?
Contact your QSA for direction. Note that First Data does validate application name and version for PA-DSS/PCI compliance before
releasing any product into production.
About Ambimat Electronics:
With design experience of close to 4 decades of excellence, world-class talent, and innovative breakthroughs, Ambimat Electronics is a single-stop solution enabler to Leading PSUs, private sector companies, and start-ups to deliver design capabilities and develop manufacturing capabilities in various industries and markets. AmbiIoT design services have helped develop Smartwatches, Smart homes, Medicals, Robotics, Retail, Pubs and brewery, Security.
Ambimat Electronics has come a long way to become one of India’s leading IoT(Internet of things) product designers and manufacturers today. We present below some of our solutions that can be implemented and parameterized according to specific business needs. AmbiPay, AmbiPower, AmbiCon, AmbiSecure, AmbiSense, AmbiAutomation.
To know more about us or what Ambimat does, we invite you to follow us on LinkedIn or visit our website.