Ambisecure key
AmbiSecure Key – Security Digital USB Key
The AmbiSecure Key is a hardware-based authentication solution that is FIDO2 standard compliant. The Key is used to provide a simple and highly secure sign-in feature to any online server supporting FIDO authentication algorithm and enables compliance requirements for strong authentication.
Now that passwords are fast becoming obsolete and your privacy, as well as the security of your digital profile, is very often compromised it is necessary to up the anté with hardware security.
Strong Authentication:
Authentication via cryptographic proof instead of shared secrets, robust protection against phishing and MITM attacks. The U2F protocol provides strong authentication without requiring a complex backend or framework to support it. Turning traditional authentication on its head, FIDO U2F makes the authentication device, like the AmbiSecure Key.
Flexibility:
The AmbiSecure Key provides a simple and intuitive authentication experience that users find easy to use, ensuring rapid adoption and organizational security. Ambisecure Keys do not require a battery or network connectivity, making authentication always accessible.
Plugin and Use:
The AmbiSecure Key Series helps organizations accelerate to a passwordless future by providing support for the FIDO2 protocol. FIDO standard security key is simple to use. You plug it in and tap the button to activate—no codes to input and no software to run.
Features:-
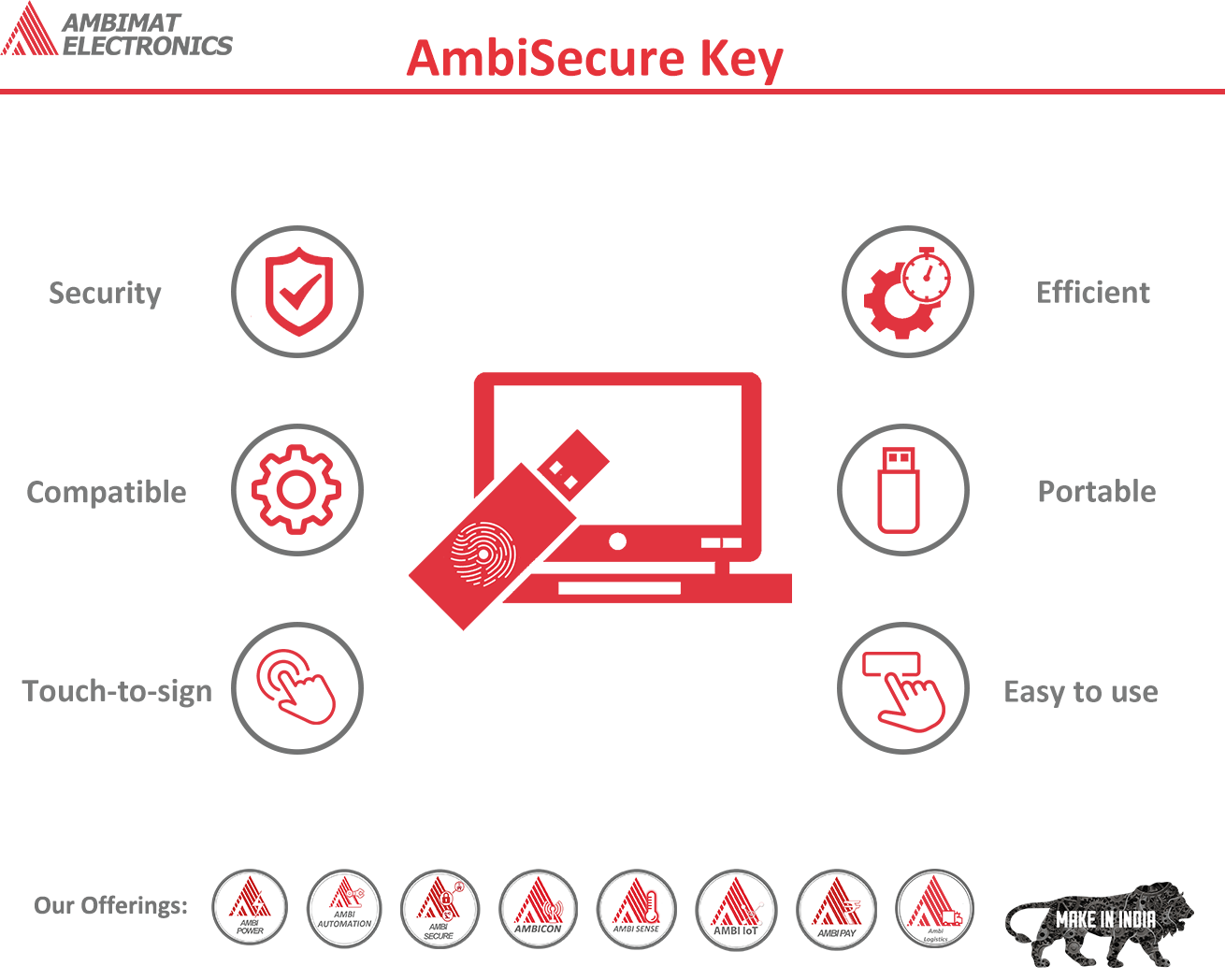
Easy to Use
No battery or network connectivity required, users simply insert and tap to authenticate
Touch-to-Sign
Establish user presence, and prevent remote takeovers, with a simple touch on the AmbiSecure Key during login
Security
AmbiSecure Key provides the user a secure authentication
Efficient
Reduce password reset or account lockout queries.
COMPATIBLE
AmbiSecure Key fits into any standard USB port
PORTABLE
Fit AmbiSecure Key on a keyring and carry without any worry
SPECIFICATIONS:
| Supported Operating Systems | : Windows, Linux, macOS, iOS, Android |
| USB Type | : USB-A/C |
| NFC-enabled | : Yes |
| Authentication Methods | : Passwordless, Strong Two Factor Authentication |
| Identity & Access Management | : Any FIDO compliant cloud |
| Password Managers | : Can be provided on request |
| Function | : FIDO2, U2F |
| Certifications | : FIDO2 Certification (Underway) |
| Cryptographic Specifications | : ECC P256 |
| Design & Durability | : Rugged enclosure, No batteries required, No moving parts |
| Device Type | : USB HID Device |
| Single Sign ON | : Supported (Currently under development) |