Dear Readers,
This week’s blog is about how the cost of passwords is seen as a necessary evil. However, they present too many risks to ignore. For starters, passwords are too easy to steal and guess. The 2021 Verizon Data Breach Investigations Report confirms this, finding that 61% of breaches in 2020 were executed using unauthorized credentials. Despite efforts to increase password security awareness and strengthen policies, users rely on poor and risky password practices.
Given the security risks and usability problems that passwords present, passwordless authentication is a far better and safer method of ensuring only the right people have access to the right things and for the right reasons.
Ambimat Electronics, with its experience of over forty years, desires to draw the attention of its readers and potential customers towards this blog post about their new product called AmbiSecure key and how it will benefit us.
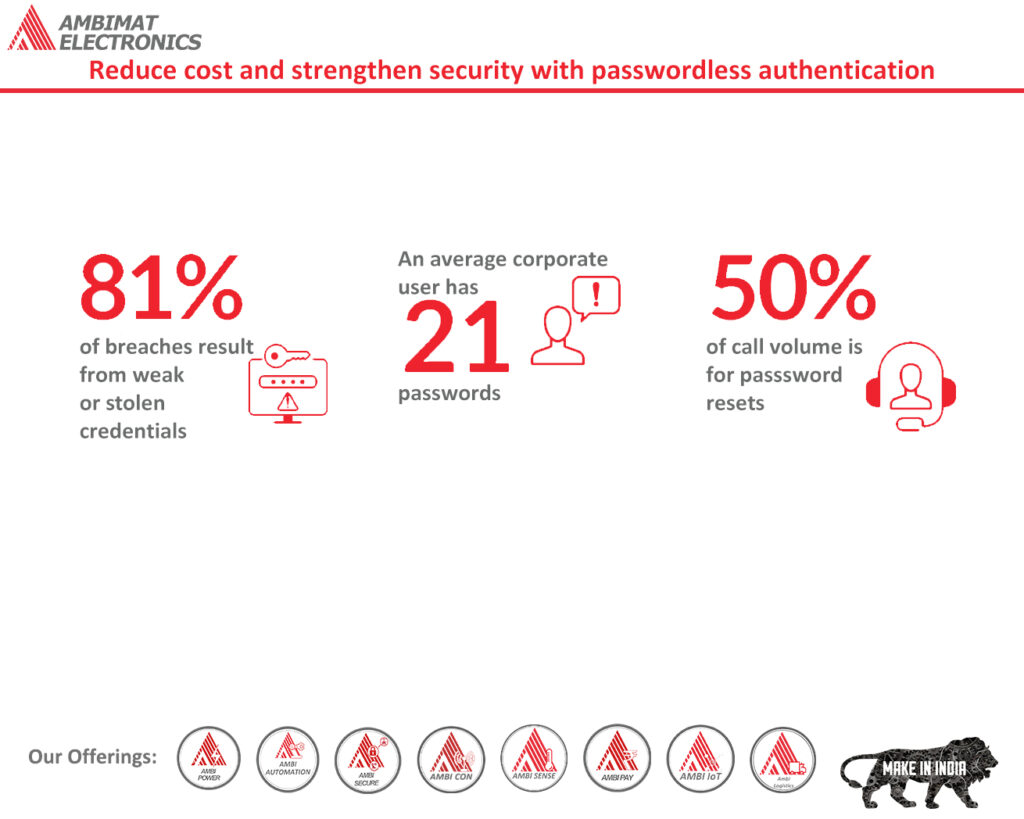
Reduce cost and strengthen security with passwordless authentication
By now we all have understood that passwords are characteristically insecure. Moreover, they are expensive to manage. Remembering the password is a challenging process, especially if they are too complex. However, they are solutions above and beyond passwords such as FIDO2 security keys and authenticator apps, which provide users with more secure and convenient login methods. Careful planning and time are important when it comes to passwordless implementation. Most of us often wonder how much time it will take to reap the benefits of passwordless. We shall examine:
- How privacy is safeguarded and security is strengthened with biometric
- The cost reduction realized from passwordless transition
- Steps to be taken for passwordless preparation and strengthening the security of an organization
Biometrics safeguards user privacy and improves security
The main objective of passwords, or any authentication protocol is to verify user identity. However, it does not necessarily mean that whoever is entering the password, is the person they claim to be. According to Verizon Data Breach Report “, Eighty-one percent of breaches happen due to weak and compromised passwords”. Therefore, the ultimate verdict is that passwords solely cannot be unique identifiers.
A better option is required to identify users and improve security. Biometrics is one such method. Fingerprints, face, voice, and iris are unique to users — nobody else will have similar features. Many passwordless solutions rely on biometrics as an alternative to passwords because biometrics are considered to identify users accurately.
Like personal identifying information (PII), biometrics has privacy issues. Many users have the opinion that technology organizations that collect such information can make them available to other entities. Or biometric data can be stolen. For this reason, companies who are a part of the FIDO Alliance came up with the solution of the FIDO2 standard that heightens security concerning credentials. Users can rest assured that no FIDO2-compliant company views, stores, or transfers user biometric data or images.
This is how it works:
- When a biometric login is created by a user, systems and platforms use an algorithm to create one-of-its-kind identifiers which are stored on the device — encrypted, secure, and never shared.
- As and when the user logs in, the biometric is associated with the unique identifier
- The user is authenticated when a match is met
Reduce costs, improve security, and increase productivity
Let us now consider the cost related to passwords. For this, we can use the example of a tech giant such as Microsoft’s own experience when implementing passwordless for its users. As tech companies like Microsoft began their journey towards passwordless, most of its users refrained from using passwords to authenticate themselves to organization systems, resources, and applications. It has reduced costs, but it is well protected as well.
Because passwords are often forgotten, the cost to reset them is quite significant and high. Tech giant such as Microsoft incurs soft costs with every password reset. This is also associated with productivity loss as users cannot log in. Hard costs are also incurred when the company’s helpdesk administrator helps a user reset their credential.
As we have taken Microsoft as an example, let us now look at the cost estimated before they rolled out with passwordless authentication:
- Hard costs were estimated at $3 million a year.
- Lost productivity costs about $6 million a year.
Microsoft reported the following benefits after shifting to passwordless:
- Hard cost and soft cost were reduced by 87%.
- As there is a reduction in company cost, the cost to hackers increases and there it is less of a target.
Multi-factor authentication is the starting point for going passwordless
Those companies thinking of rolling out passwordless in a few years or if they are already doing so, then these steps will help them get ready.
Step 1: Outline password and biometric strategy — To help meet accessibility needs and give users more options, organizations should choose more than one biometric factor for authentication needs.
Step 2: Shift identities to the cloud — To protect identities, uncover breach patterns, and recover from a breach, user behavior analytics and security intelligence should be
leveraged.
Step3: Enable Multi-factor authentication (MFA) — Using one or more factors to verify multi-factor authentication increases security over and above passwords. Account compromise is reduced with the use of MFA. The risk of the password being removed in passwordless authentication as a biometric identifier is one factor while the device possession is another.
Step4: Pilot passwordless — Organization should run a pilot test for passwordless for the riskiest group of users, before full implementation.
An organization that isn’t still ready to go passwordless can enable MFA to reduce a breach. Do not use passwords that can be guessed easily. Last, but not least organizations can implement password solutions such as FIDO2 security keys. They can help accomplish the following:
- Stronger security.
- Reduced costs over time.
- Increased attacker costs.
- More productive users.
Strengthen Security with AmbiSecure
FIDO2 is a standard that simplifies and secures user authentication. It uses public-key cryptography to protect from phishing attacks and is the only phishing-proof factor available. Corporations around the world and across many sectors, including healthcare, can benefit from Fast Identity Online or Fast ID Online (FIDO) authentication, which their employees and users can use to minimize security risks and improve overall user experience. The AmbiSecure key and card are FIDO certified which offers superior security by combining hardware-based authentication and public key cryptography to effectively defend against phishing attacks and eliminate account takeovers.
AmbiSecure helps organizations accelerate to a password-less future by providing FIDO2 protocol support. Not only does FIDO2 supports two-factor authentication, but also paves the way for eliminating weak password authentication, with strong single-factor (passwordless) hardware-based authentication. The AmbiSecure provides a simple and intuitive authentication experience that users find easy to use, ensuring rapid adoption and organizational security. Ambisecure key or card does not require a battery or network connectivity, making authentication always accessible.
About Ambimat Electronics:
With design experience of close to 4 decades of excellence, world-class talent, and innovative breakthroughs, Ambimat Electronics is a single-stop solution enabler to Leading PSUs, private sector companies, and start-ups to deliver design capabilities and develop manufacturing capabilities in various industries and markets. AmbiIoT design services have helped develop Smartwatches, Smart homes, Medicals, Robotics, Retail, Pubs and brewery, Security.
Ambimat Electronics has come a long way to become one of India’s leading IoT(Internet of things) product designers and manufacturers today. We present below some of our solutions that can be implemented and parameterized according to specific business needs. AmbiPay, AmbiPower, AmbiCon, AmbiSecure, AmbiSense, AmbiAutomation.
To know more about us or what Ambimat does, we invite you to follow us on LinkedIn or visit our website.
References:-
Reference:-
https://www.microsoft.com/security/blog/2019/12/11/go-passwordless-strengthen-security-reduce-costs/