Dear Readers,
This week’s blog is about Why use Multi-factor Authentication (MFA).
By being agile in adopting and deploying efficient security measures like MFA, you can help your business stay agile and competitive in a tight market. The use of multi-factor authentication is vital, as it ensures that information is only accessed by the intended person, making it harder for cybercriminals to steal. If user data is less tempting, cyber thieves will go for a different one. Multi-factor authentication is a blend of two different factors. One is usually the username and password, which is something the user knows.
Ambimat Electronics, with its experience of over forty years, desires to draw the attention of its readers and potential customers towards this blog post about their new product called AmbiSecure key and how it will benefit us.
Why use Multi-factor Authentication (MFA)
Cybercriminals have billions of records to steal from. If they even choose one, they can take control of banks accounts, health records, organizational secrets, and much more.
The use of multi-factor authentication is vital, as it ensures that information is only accessed by the intended person, making it harder for cybercriminals to steal. If a user data is less
tempting, cyber thieves would go for a different one.
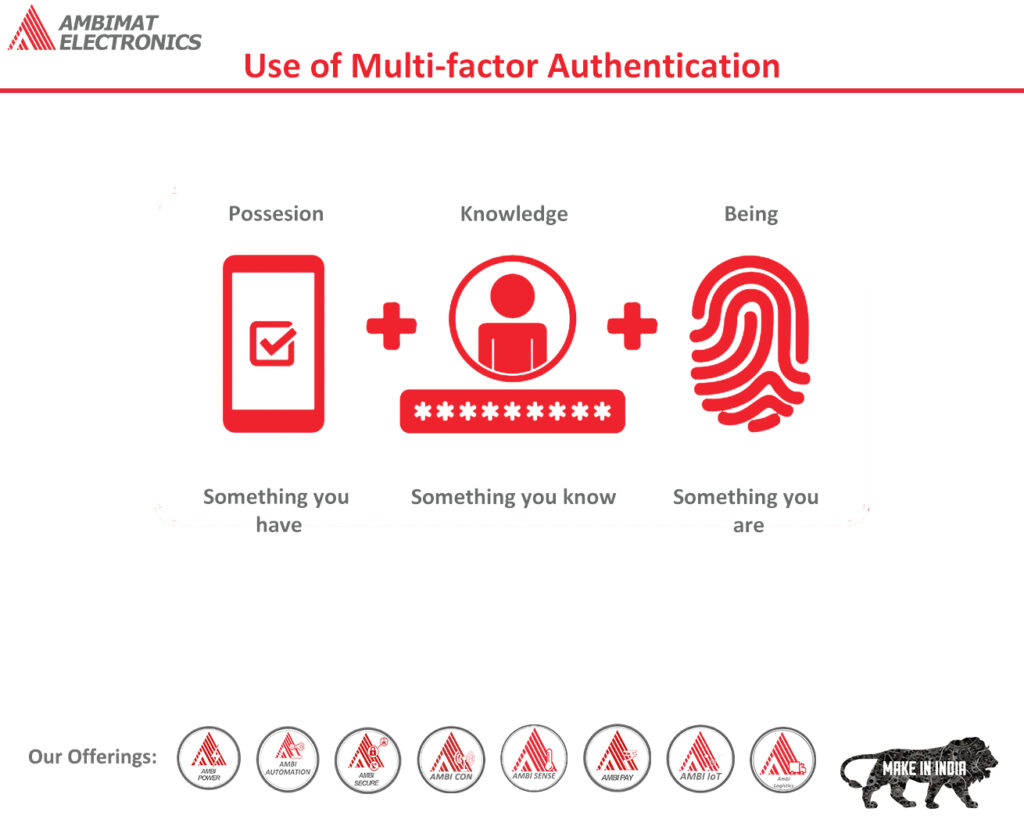
Multi-factor authentication is a blend of two separate factors. One is usually the username and password, which is something the user knows. The other is:
Something the user has: This could be a mobile device, keycard, or USB.
Something the user is: This is typically biometric such as fingerprints, facial recognition, voice, and iris scan that defines the user characteristics.
Adding this secondary layer of protection to user passwords protects their privacy. Setting it up and using it does not take much time.
Does Password Provide Enough Security?
Whether it is our email, bank records, or work database, without passwords we are unable to log into our accounts. Passwords have truly become a part of our lives, and even today, many users frequently change their passwords hoping that it would keep their information safe. Unfortunately, we have to face the fact that passwords alone are not adequate to provide us with the appropriate safety level.
Take for instance the Google account. One password gives access to a vast number of services, such as calendar, YouTube, email, and other apps associated with google. Cyber thieves only require one password, and they would have access to several different accounts as well.
Data breaches are not limited to just emails and bank frauds. The health sector is also a target for cybercriminals. Once they obtain access to medical records, they can manipulate data to bill fraudulent companies to make money. It is difficult to revert an altered medical record, and this alteration can affect user health care and credit ratings.
Today, many companies are now understanding the risk associated with cyber-attacks and are taking appropriate action. They are inclining towards the use of multi-factor authentication to protect user identity and information. If this authentication is not yet implemented, it is time to act now.
How does Multi-factor Authentication work?
In most MFA solutions, passwords are not eliminated. They are simply protected by an additional security factor that verifies the user claiming to be who they are, and keeps unauthorized persons at bay.
The MFA process includes:
Registration: A user links their device such as a keycard, USB key, or mobile device to the
system and declares that the device belongs to them.
Login: This is where the user enters their login credentials such as a password.
Verification: The system connects to the user’s device. They might receive a verification code on their mobile device or may need to insert their USB key or use the keycard over an NFC reader.
Reaction: the process is complete with the verified device. Entering the PIN or code comes next.
A user’s device registers the verification, and as a result not required always. However, if the user uses a device other than their own, verification may be required at each login.
It can be noticed from above that although multi-factor authentication looks simple enough, it is quite effective in keeping accounts safe from unwanted risks. Therefore, shifting towards multi-factor authentication could protect user security in a big way.
Multi-factor Authentication with AmbiSecure
FIDO2 is a standard that simplifies and secures user authentication. It uses public-key cryptography to protect from phishing attacks and is the only phishing-proof factor available. Organizations around the world and across many sectors can benefit from Fast Identity Online or Fast ID Online (FIDO) authentication, which their employees and users can use to minimize security risks and improve overall user experience. The AmbiSecure key and card are FIDO certified which offers superior security by combining hardware-based authentication and public key cryptography to effectively defend against phishing attacks and eliminate account takeovers.
AmbiSecure helps organizations accelerate to a password-less future by providing FIDO2 protocol support. FIDO2 supports two-factor authentication and multi-factor authentication. It also paves the way for eliminating weak password authentication, with strong single-factor (passwordless) hardware-based authentication. The AmbiSecure provides a simple and intuitive authentication experience that users find easy to use, ensuring rapid adoption and organizational security. Ambisecure key or card does not require a battery or network connectivity, making authentication always accessible
About Ambimat Electronics:
With design experience of close to 4 decades of excellence, world-class talent, and innovative breakthroughs, Ambimat Electronics is a single-stop solution enabler to Leading PSUs, private sector companies, and start-ups to deliver design capabilities and develop manufacturing capabilities in various industries and markets. AmbiIoT design services have helped develop Smartwatches, Smart homes, Medicals, Robotics, Retail, Pubs and brewery, Security.
Ambimat Electronics has come a long way to become one of India’s leading IoT(Internet of things) product designers and manufacturers today. We present below some of our solutions that can be implemented and parameterized according to specific business needs. AmbiPay, AmbiPower, AmbiCon, AmbiSecure, AmbiSense, AmbiAutomation.
To know more about us or what Ambimat does, we invite you to follow us on LinkedIn or visit our website.