Dear Readers,
This week’s blog is about User experience with passwordless authentication.
Passwords require ongoing management from both users and IT staff. For the average user, keeping track of ever-multiplying passwords of varying complexity is, at minimum, a hassle and often a challenge. Forgotten passwords can delay work or trigger account lockouts. Users often reuse passwords across accounts or write them down to aid memory, further compromising an already weak system. Password reuse can also multiply the impact of hijacking, phishing, and data breaches, making it possible for an attacker to unlock multiple accounts with a single stolen password.
Given the security risks and usability problems that passwords present, passwordless authentication is a far better and safer method of ensuring only the right people have access to the right things and for the right reasons.
Ambimat Electronics, with its experience of over forty years, desires to draw the attention of its readers and potential customers towards this blog post about their new product called AmbiSecure key and how it will benefit us.
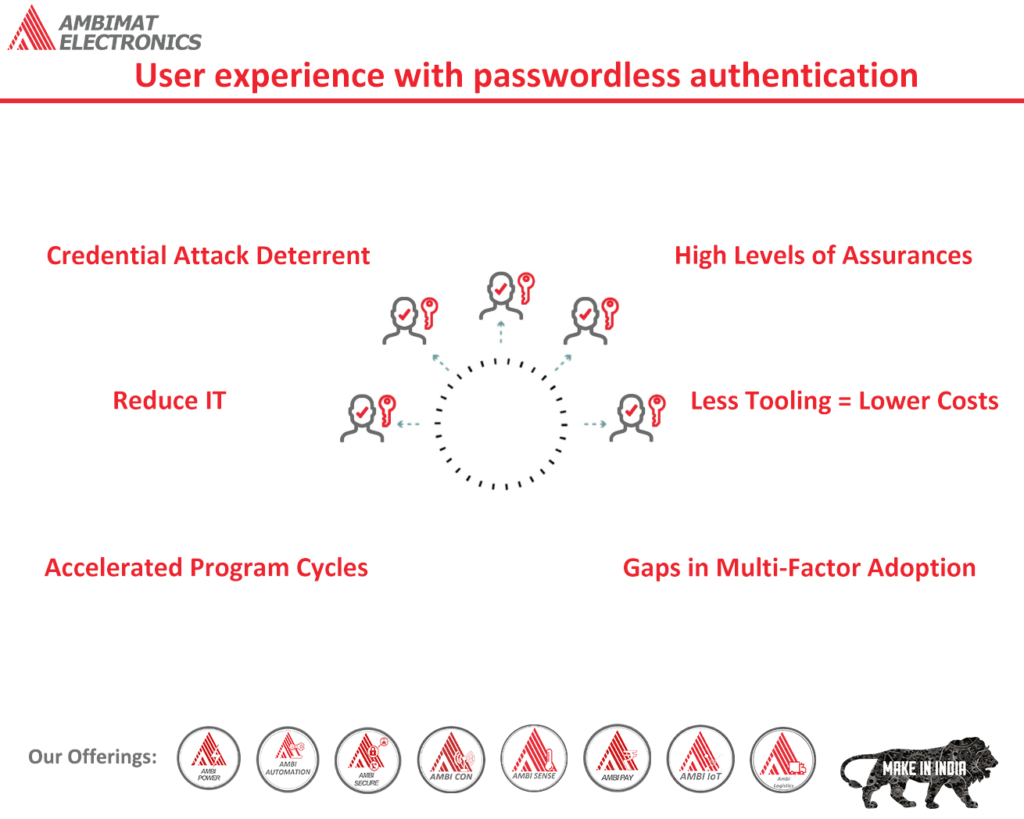
User experience with passwordless authentication
Passwordless authentication means that a user can access applications and systems without having to enter passwords or answer a security question. An alternative form of evidence could be a fingerprint, proximity badge, or hardware token code. For a streamlined user experience, strong security, and reducing IT costs and complexity, passwordless authentication is used in conjunction with multi-factor authentication (MFA) and single sign-on (SSO) solutions.
The problem with passwords
To perform their jobs, many employees rely on a wide range of digital applications. With such a job description comes the hassle of memorizing and tracking frequent password changes. Overwhelmed with such procedure, many employees take a short way out, such as using similar passwords for all applications, uncomplicated passwords, or posting them on a sticky note. This is a bad password management practice that allows bad actors to mount attacks and steal vital information. In reality, account breaches happen due to compromised credentials.
Password-based authentication is simply vulnerable. With the sophisticated technology, attackers can easily guess user credentials and can gain access to confidential data and systems. Some techniques they use are as follows:
- Brute force: In this method, bad actors use programs that can generate a random username and password combinations or exploit weak passwords.
- Credential Stuffing: Account credentials that are compromised is used to gain access to another account as many users use a similar password for multiple accounts.
- Phishing: A phishing attack is an act of sending fraudulent messages designed to trick the user into giving their log-in credentials and sensitive information, or to deploy malicious software on the user’s system.
- Keylogging: In this method, malware is installed in the user’s system which allows criminals to capture keystrokes.
- Man-in-the-middle attacks: Threats actors can portray as a legitimate source to intercept communication over public WIFI and steal credentials.
Passwordless authentication improves user experience and reduces risk
Passwordless-based authentication strengthens security by eradicating bad password management practices and reducing attacks avenues. It provides a seamless user experience by removing password fatigue. Passwordless Authentication works by eliminating the need to memorize passwords and security questions and allows users to access applications and services with other authentication methods such as:
- FIDO2-compliant devices, hardware security keys, proximity badges, or physical tokens.
- Biometrics, such as fingerprints, voice input, facial recognition, and iris scan.
- Mobile authenticator app.
- Software tokens and certificates.
Employees can use proximity badges, security tokens, or mobile apps for single sign-on and secure access to enterprise applications and services through passwordless authentication. Passwordless-based Authentication is also often executed as part of an MFA solution, where users are required to provide evidence in several forms to gain access to enterprise applications and systems. The remote user, for example, might need to tap a fingerprint sensor and enter a short-lived SMS code to log into their mobile app.
Modern multi-factor authentication solutions use contextual information (such as location, time of day, IP address, device type, etc.) and business rules to decide which authentication factors to use for a specific user in a particular scenario. An employee trying to get access to an enterprise application from a reliable home computer might only be required to provide one form of authentication under adaptive MFA. However, an SMS code may be required to access the app if the user is accessing an application from outside over an unsecured WIFI connection.
Benefits of Passwordless Authentication
There are several functional and business benefits associated with passwordless authentication:
- Streamlined user experiences: Passwordless authentication provides a seamless user experience by removing password fatigue for all applications and services.
- Enhanced Security: It removes the practice of bad password management, hence, reducing credential theft and impersonation.
- Streamlines IT operations: By removing the need to issue, secure, reset, rotate, and manage passwords.
AmbiSecure provides a seamless user experience
FIDO2 is a standard that simplifies and secures user authentication. It uses public-key cryptography to protect from phishing attacks and is the only phishing-proof factor available. Corporations around the world and across many sectors, including healthcare, can benefit from Fast Identity Online or Fast ID Online (FIDO) authentication, which their employees and users can use to minimize security risks and improve overall user experience. The AmbiSecure key and card are FIDO certified which offers superior security by combining hardware-based authentication and public key cryptography to effectively defend against phishing attacks and eliminate account takeovers.
AmbiSecure helps organizations accelerate to a password-less future by providing FIDO2 protocol support. Not only does FIDO2 supports two-factor authentication, but also paves the way for eliminating weak password authentication, with strong single-factor (passwordless) hardware-based authentication. The AmbiSecure provides a simple and intuitive authentication experience that users find easy to use, ensuring rapid adoption and organizational security. Ambisecure key or card does not require a battery or network connectivity, making authentication always accessible.
Reference:-
https://www.cyberark.com/what-is/passwordless-authentication/