Dear Readers,
This week’s blog is about how organizations are being forced to move away from passwords. As our digital footprints grow day by day, maintaining passwords itself is a tedious job. To keep it easy, users employ single passwords across applications. Data breaches and hacks these exposed users across platforms and placed enterprises at risk. So, a more straightforward, more robust, user-friendly authentication method is the need of the hour. Passwordless helps to accurately verify the user’s identity and eliminate the risk of compromised credentials.
Today, organizations are moving towards passwordless authentication, using advanced technologies such as biometric signatures, hardware tokens, cryptographic keys, or PINS to verify users.
The use of multi-factor authentication is vital, as it ensures that information is only accessed by the intended person, making it harder for cybercriminals to steal. If user data is less
tempting, cyber thieves will go for a different one. Multi-factor authentication is a blend of two different factors. One is usually the username and password, which is something the user knows.
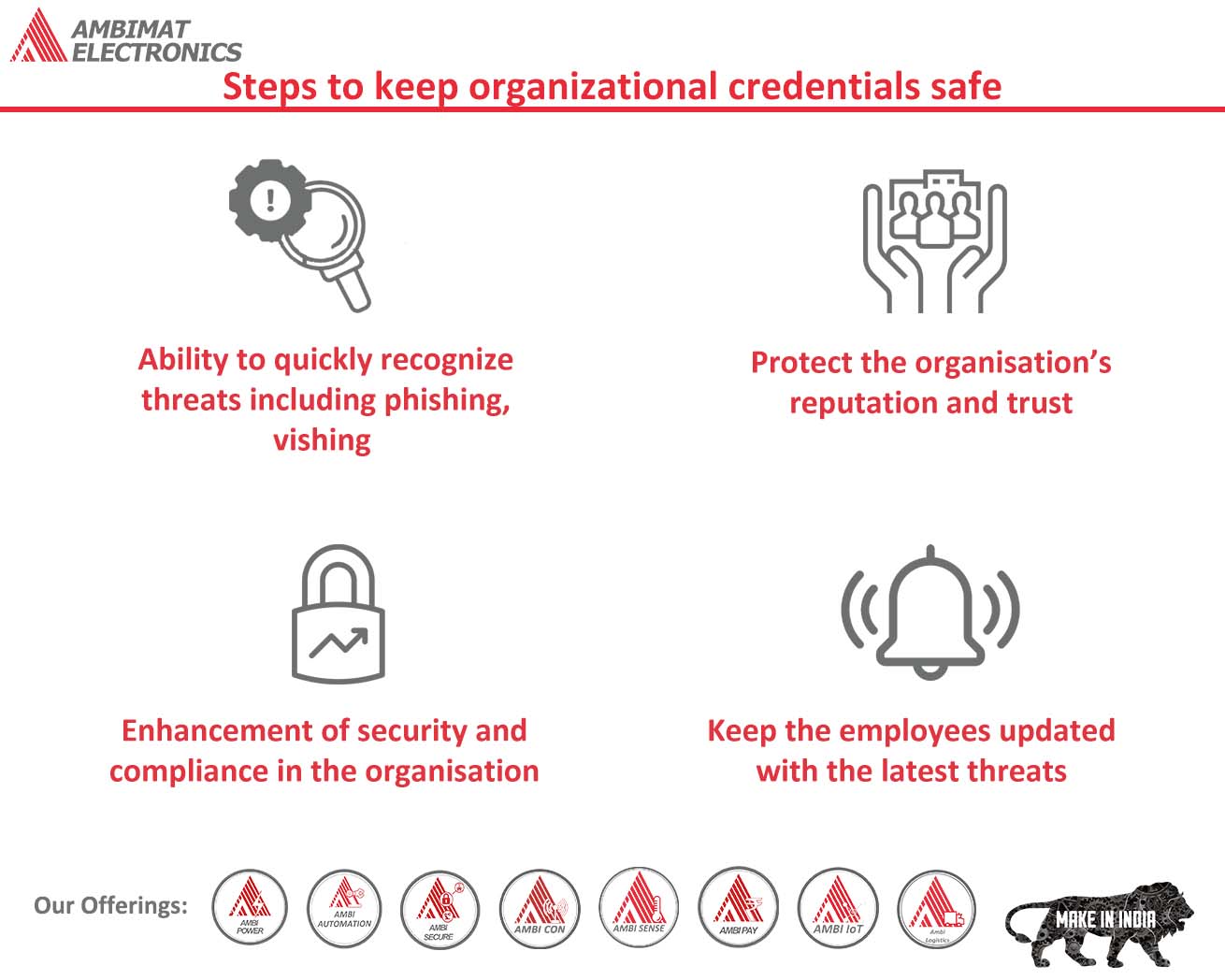
Steps to keep organizational credentials safe
Ambimat Electronics, with its experience of over forty years, desires to draw the attention of its readers and potential customers towards this blog post about their new product called AmbiSecure key and how it will benefit us.
Stolen corporate credentials are often put up for sale on the dark web. The asking price of such a credential depends on several factors, one of them being the revenue generated by the corporation. On the other hand, a ransomware attack can fetch cybercriminals a staggering amount in ransom.
The implication of corporate credentials exposed on the dark web is not just limited to financial loss. With cybercriminals gaining easy access to organizational login details, damaged reputation, loss of intellectual property, and increased insurance premiums follow as well.
Fortunately, there are methods that corporates can adopt to prevent their credentials from landing up for auction on the dark web. Follow the below six steps to ensure that organizational credentials remain secure.
1) Use unique passwords for applications and systems
If passwords are still in use, the organization needs to educate its employees to use different passwords for different applications, systems, and accounts.
For decades, corporates have been advised by cybersecurity professionals on the importance of strong and unique passwords. Sadly, even with warnings, reusing password remains a common practice. A survey conducted by LastPass1 showed that an average employee is likely to use the same password about 13 times. Even worse, these passwords tend to be weak and compromised easily.
Another breach report by SpyCloud showed that employees of large corporations used passwords, such as “123456”, “password”, or the name of the company they work for.
The foremost thing organization can do is have a stricter policy in respect to using “bad passwords”. To get a better picture of which password should be restricted, organizations can refer to NordPass’s “Top 200 most common password in 2020”.
In most scenarios, employees who are expected to maintain too many passwords and having each a unique one and still remember them is not exactly a reality. In this situation, the organization should enable password managers for both personal and professional use. This will tremendously reduce the likelihood of employees reusing the same password across multiple devices and applications. Moreover, 73% of workers3 duplicate their password across corporate networks and personal accounts, making it easy for hackers to gain access to them. Therefore, having this approach is very critical.
2) Change passwords regularly
Even while maintaining a systematic approach to secure passwords, they can appear on the dark web. It is noted that at least one data breach is experienced by 53% of organizations as a result of compromised credentials.
Companies should form a policy for their employees to change their passwords frequently — every few months. Such a habit will ensure that credentials appearing on the dark web does not remain fresh, and cybercriminals can no longer use them.
3) Use Multi-factor authentication
Enabling multi-factor authentication can reduce and block account takeovers.
By adding a layer of protection over and above traditional passwords, multifactor authentication makes it difficult for hackers to impersonate someone to gain access to accounts. Even if a pernicious being managed to get hold of a user password, they won’t be able to log in to their corporate network as MFA is enabled.
Although MFA does provide protection, not all MFA are built equal, especially SMS MFA. Hackers have sophisticated tools that can be used to spoof, intercept, and phish short message services (SMS).
4) Educate Employees on Safety Awareness
Human error is the root of cybersecurity repercussions. This is why employees are often considered the weakest link in a company’s security landscape. Employees are tricked into revealing their credentials and organizational details through phishing scams.
To mitigate risk, it is crucial to educate employees on how to recognize threats. Apart from lectures, another method should be used to make training effective. Many employees have become victims of phishing attacks because of legitimate-looking emails. Therefore, employees should be familiarized with real-world phishing attacks and other password hacks to protect themselves better.
Hackers can avail all the information they require through social media accounts by crafting a legitimate-looking email. Hence, employees should also be trained in managing their social
media accounts and virtual private network (VPN) when working remotely. Oversharing information online should also be discouraged.
5) Monitor the dark web
There are tools available for organizations to use if they suspect that their credentials are exposed on the dark web. Many of such tools are free and can perform dark web scans to check if an organization’s asset is in danger or not.
Data breaches are a recurring thing and therefore, scanning the dark web frequently is considered a best practice. Organizations can save time by investing in dark web monitoring software.
As the name implies, the monitoring system can scan the dark web on its own. It provides an alert if any credentials are up for auction that belongs to the organization. Such alerts are useful in preparing to combat such threats before sensitive credentials are used maliciously.
6) Go passwordless
With breaches happening due to compromised credentials, it is no longer safe to rely on passwords. For this particular reason, many organizations are shifting towards newer technologies for authentication — passwordless authentication.
Because users do not require to enter passwords or any other secrets to access their accounts is the sole reason passwordless is more secure — if there are no passwords, then there is nothing to steal. Users can prove their identity with the use of hardware security keys or biometrics, such as a fingerprint (high-level security).
As passwords are annoying, need to be memorized, or frequently changed, many users find it overwhelming. Passwordless authentication does not only improves the overall security landscape but also provides a seamless user experience. With this in mind, corporates are now on the verge to eliminate passwords.
Passwordless authentication is cost-effective, as it tends to lower the organizational cost incurred due to password reset calls to the IT department. It also provides better visibility over identity and access management (IAM).
So, there you have it the top six methods by which organization can prevent their credential from appearing on the dark web and reduce accounts takeovers and ransomware.
Protect corporate credentials with AmbiSecure
FIDO2 is a standard that simplifies and secures user authentication. It uses public-key cryptography to protect from phishing attacks and is the only phishing-proof factor available. Corporations around the world and across many sectors, including healthcare, can benefit from Fast Identity Online or Fast ID Online (FIDO) authentication, which their employees and users can use to minimize security risks and improve overall user experience. The AmbiSecure key and card are FIDO certified which offers superior security by combining hardware-based authentication and public key cryptography to effectively defend against phishing attacks and eliminate account takeovers.
AmbiSecure helps organizations accelerate to a password-less future by providing FIDO2 protocol support. Not only does FIDO2 supports two-factor authentication, but also paves the way for eliminating weak password authentication, with strong single-factor (passwordless) hardware-based authentication. The AmbiSecure provides a simple and intuitive authentication experience that users find easy to use, ensuring rapid adoption and organizational security. Ambisecure key or card does not require a battery or network connectivity, making authentication always accessible.
References:
https://www.lastpass.com/state-of-the-password/global-password-security-report-2019
https://nordpass.com/most-common-passwords-list/
https://securityboulevard.com/2020/06/automation-in-compliance-why-its-a-business-imperative-and-where-to-start/
https://www.microsoft.com/security/blog/2019/08/20/one-simple-action-you-can-take-to-prevent-99-9-percent-of-account-attacks/