Dear Readers,
This week’s blog is about Tightening your security and how passwords are the keys to most devices and almost everything you do online. Unfortunately, even the best passwords can get hacked, stolen, or unintentionally shared. But fortunately, there is an easy way to add another layer of protection and your username and password to make your login more secure.
The use of multi-factor authentication is vital, as it ensures that information is only accessed by the intended person, making it harder for cybercriminals to steal. If user data is less
tempting, cyber thieves will go for a different one. Multi-factor authentication is a blend of two different factors. One is usually the username and password, which is something the user knows.
Ambimat Electronics, with its experience of over forty years, desires to draw the attention of its readers and potential customers towards this blog post about their new product called AmbiSecure key and how it will benefit us.
Security Tips: For Developers, By Developers
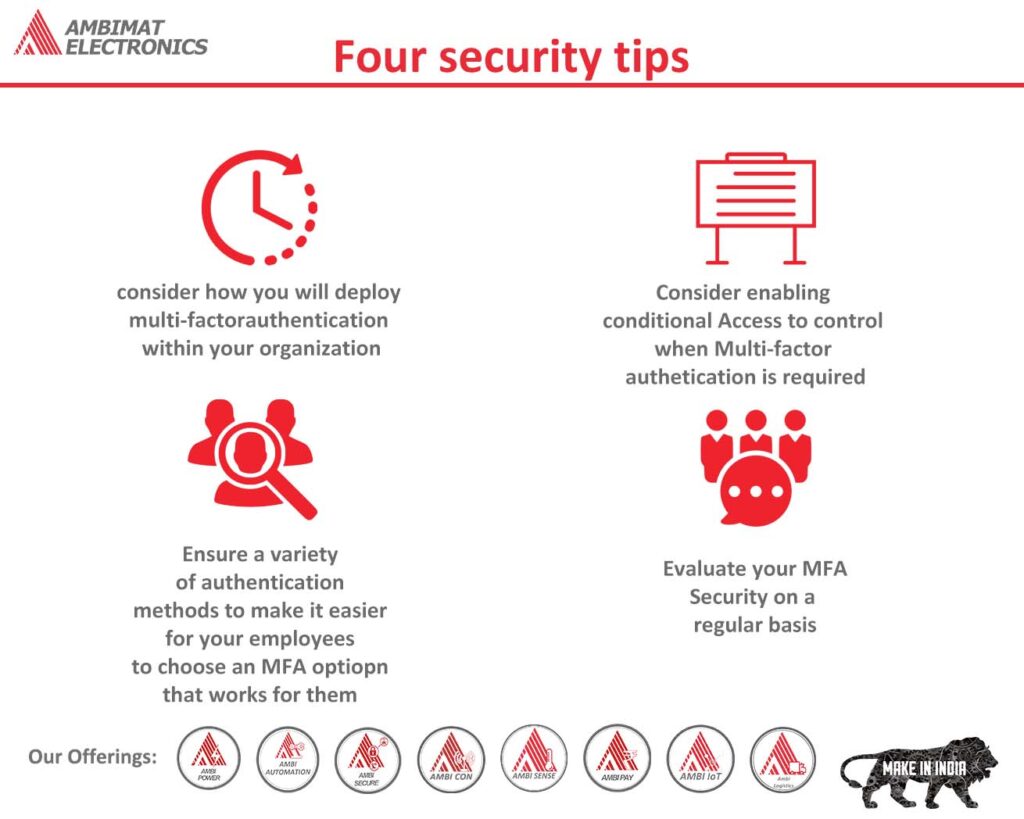
These are some facts on what the developer community can do to keep themselves cyber smart all year long, even with the end of National Cybersecurity Awareness Month. We have already discussed access management and how users can protect their accounts. Today, we are going to offer tips from our developer team to other developers looking to enhance their security game.
The most ideal approach is to secure oneself first, before helping others. This can be achieved through the use of password manager or enabling two-factor and multi-factor authentication across all personal and work accounts.
Let us now get into more technical things:
1) The first and foremost thing to do is encrypt operating and development environments. There is a tool to achieve this, such as AmbiSecure, it provides secure protection for work systems. The solution is simple to use as it very convenient and transparent to authorized and authenticated users. Using a hardware security key, AmbiSecure supports two-factor authentication to further strengthen security.
2) Developer tools that use multi-factor authentication should be used to code signing certificates and data secure. Several hardware security keys have the ability to store code signing certificate and can be used to sign code. Apart from supporting FIDO authentication protocols, many keys also support OpenPGP; ECC support is one of the enhancements to the OpenPGP implementation.
3) Attacks are inevitable because weak points exist in personal accounts. However, security can be spread across all devices, and not just corporate network.
“Due to the rise of bring-your-own-device (BYOD) and employees working from home, the attack point has moved from corporate grids to endpoints. Therefore, security measures should consider all terminals including mobile devices”
Hot tip to support hardware security key into a product:Ready-to-use animation is available to assist users on how to use hardware security keys, and how smartphones can work as an NFC device. With SDK availability for hardware security, Developers of Android application can enable strong, hardware-backed keys for security to leverage modern authentication protocols, such as Universal Second Factor (U2F).
4) It is not necessarily hard to implement strong authentication for users. It is advisable to take full advantage of modern protocols such as FIDO2 or Webathon with hardware security keys. It is noted that a number of use cases has been brought by companies around the world. Websites, email address, SSL certificates use domain names and therefore, they are valuable asset to individuals, enterprises, and businesses. Two-factor authentication with a hardware security key ensures only authorized users gain access to accounts.
“The objective of hardware security key vendor is to keep enterprise and customers protected as they are linked to their domain. It is necessary to stay ahead in the game by providing cutting edge security technology is essential to the mission.
“Application developers should always think about integrating security into their projects, products, and services. Almost all hardware security manufacturer provides guides and resources to other developers through their developer program. Beside this, access to SDKs to integrate with their project is also available.
Developers Program with AmbiSecure
FIDO2 is a standard that simplifies and secures user authentication. It uses public-key cryptography to protect from phishing attacks and is the only phishing-proof factor available. Corporations around the world and across many sectors, including healthcare, can benefit from Fast Identity Online or Fast ID Online (FIDO) authentication, which their employees and users can use to minimize security risks, and improve overall user experience. The AmbiSecure key and card is FIDO certified which offers superior security by combining hardware-based authentication and public key cryptography to effectively defend against phishing attacks and eliminate account takeovers.
AmbiSecure helps organizations accelerate to a password-less future by providing FIDO2 protocol support. Not only does FIDO2 supports two-factor authentication, but also paves the way for eliminating weak password authentication, with strong single-factor (pass wordless) hardware-based authentication. The AmbiSecure provides a simple and intuitive authentication experience that users find easy to use, ensuring rapid adoption and organizational security. AmbiSecure key or card does not require a battery or network connectivity, making authentication always accessible.
References:
https://www.yubico.com/blog/4-security-tips-for-developers-by-developers/